This page will show you how to work at home as if sitting in front of CS Linux computers at Rutgers, Access Files from CS Systems, Set up Online Meetings using Rutgers Zoom and WebEx, and Connect to Rutgers-only resources from home.
Rutgers OIT Remote Working Resources
To help Faculty & Students with remote instruction and other information related to learning, Internet access, and more, Rutgers has prepared Technology Resources for Students and Technology Tools for Faculty sites. For more complete info, see Remote Technology Resources, which has a wealth of information about working remotely.
Using a Graphical or Command line Linux on a CS System
There are three basic approaches if you want a GUI interface (technically, an X11 window environment). The first uses your browser. The second and third require installing a client (except on Windows, where the Microsoft Remote Desktop is already there.) The last option uses SSH. SSH is available on Macintoshes and Linux, but you must install a program on Windows.
- Weblogin. This Apache Guacamole gateway lets you get a graphical desktop on a CS Linux system or Windows machine with Remote Desktop service enabled or SSH terminal. It works in your browser. See Using CS WebLogin to Access iLab Machines
- Microsoft Remote Desktop. This is similar to WebLogin except you are using a special client. It is available for Windows, Mac, and Linux. See Remote Desktop instructions.
- Command Line. If you prefer a command-line environment, you can use ssh.
- Linux and Mac come with SSH, so from a command line window, do
ssh HOSTNAME. If your username is different at home and at Rutgers, typessh user@HOSTNAMEwith your Rutgers username - For Windows, many people use an SSH client named Bitvise SSH Client (video). It has a GUI that connects to the Linux command line. The
HOSTNAMEshould be the name of the computer you want to use. It will normally end in cs.rutgers.edu. Any of our lab computers can be used from home. However, if you don’t have a system you prefer, anyone can use ilab.cs.rutgers.edu.
- Linux and Mac come with SSH, so from a command line window, do
Online Meeting/Training Sessions
- Please do a test session to get familiar with the features you want to use.
- If you plan to do handwriting, invest in a tablet like Huion H610 Pro V2 Graphic Drawing Tablet to make writing easier.
- To improve sound quality, all participants should use a headset and avoid feedback.
- Everyone should start with a muted mic and only unmute it when conversing.
- Participants have to learn to speak one at a time.
- Consider recording your session so it can be viewed again later.
- Important: If your video conference link information is public, you are subject to interruptions known as ZoomBombing from uninvited guests.
Below are details on how to use online conferencing on each system.
Setting up Online Meetings with Rutgers Zoom
As of early July, the University has just signed a site license for Zoom. The School of Arts and Sciences recommends that people use Zoom. Zoom is a video conference tool designed for personal and corporate collaboration. It allows communication with audio, video, text chat, file sharing, whiteboard, and other features-Zoom supports for up to 300 participants. Please note that if users need to host a Zoom meeting for up to 1,000 participants, they can register for one via Microsoft Bookings.

Activation is required
Before scheduling your Zoom Session, you must activate the Zoom service by going to netid.rutgers.edu, logging, and looking for the[Service Activation] link. Click on [Zoom] and click on button at the bottom.[more details]
To learn more, click on OIT Zoom page.
Hints#1: For best experience, you should download a Zoom client for your computer or mobile device. You can start a zoom meeting using your browser by going to https://rutgers.zoom.us/.
Hints#2: When logging in using Zoom client, make sure you enter: your official Rutger Email address and click on button. Do not enter your password in the main Login page.
Setting up Online Meetings with Rutgers WebEx
University currently has a site license for Cisco Webex. Webex is a set of tools designed for personal and corporate collaboration. It is used to connect to others, typically through the internet, and allows communication with audio, video, text chat, file sharing, whiteboard, and other features. Please consult Eligibility page to see limits on different roles of users.

Activation is required
Before scheduling a Webex session, you must activate the Webex service for yourself. Go to netid.rutgers.edu, login, and look for the [Service Activation] link as shown. Click on [Rutgers Webex] and click on button at the bottom.
Personal Meeting
![]()
The default session gives you a personal meeting room. This is appropriate for a small group of people. To start a meeting, click on button.
For others to attend your meeting, share your personal meeting link which looks like https://rutgers.webex.com/join/yourNetid. For class meetings and other large gatherings, you should only use scheduled meetings or Training Sessions. You should NOT use your personal room because this link is public. This means it is subject to interruptions by uninvited guests.
More info is needed when scheduling a meeting with your personal account.
Training Sessions or Remote Instruction
![]()
For a session with a lot of attendees, for example, a class or training session, you may prefer to use a “Webex Training session.”
This is optimized for more people, gives the host the ability to share presentations, and encourages participation using whiteboard and chat.
Find the “Webex Training” link at the bottom left corner to create a training session. Click on it, and it will open a new Webex Training page.
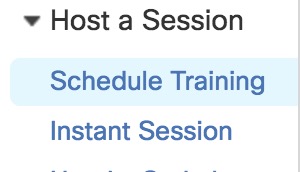
Once you get the new page, you’ll see “Host a Session” in the left bar with several options. You can [Schedule a Training] or start an [Instant Session]and other options. More info is at Getting Started with Cisco Webex Training.
Note: Do not make the password and link public. Your session could be subject to interruptions by uninvited guests. If you are using Canvas integration, this is not an issue. Otherwise, Webex recommends you use lock and unlock features to avoid this interruption.
For more info, click on below
Online Conferencing with Microsoft Teams
Rutgers Connect, known as Office 365, also allows for video conferencing via the Microsoft Teams application. Just like WebEx, Microsoft Teams works on web browsers, desktop applications, and mobile applications. OIT has created detailed documentation on how to use Microsoft Team video conferencing if you so choose.
Note: To avoid being interrupted by Teams, you should utilize the Attendee and Presenter roles.
Setting up Online Meetings with Google Meet
 Rutgers ScarletApps is essentially a G-Suite for Education products. Although it is not publicized on the ScartletApps site, ScarletApp also includes a Meeting/Conferencing feature known as Google Meet. Google Meet can be used as an alternative tool to WebEx. This license, by default, gives every user the ability to start a meeting for up to 100 participants.
Rutgers ScarletApps is essentially a G-Suite for Education products. Although it is not publicized on the ScartletApps site, ScarletApp also includes a Meeting/Conferencing feature known as Google Meet. Google Meet can be used as an alternative tool to WebEx. This license, by default, gives every user the ability to start a meeting for up to 100 participants.
During the COVID-19 crisis, Google has opened up Google Meet to G-Suite customers until July 1, 2020. This means ScarletApps users will also be able to use Google Meet to conduct meetings or training for up to 250 participants.
Instant Meeting
To set up an instant meeting, first connect to https://mail.scarletmail.rutgers.edu. Once logged in, go to https://meet.google.com. Click on button to start or join a meeting. Windows will open and ask for permission to access your camera and/or your microphone. Depending on what you want to do, click on or to start your conference.
Planned Meeting
To set up a future meeting, you need to schedule it in your Google Calendar. Please follow the Plan and Hold Meetings from Anywhere guide for details.
Accessing Files from CS Systems
If you want to work on your home machine but access files stored on our servers, there are two reasonable approaches
- sshfs, which mounts your Rutgers home directory so you can access it as if it were a disk drive on your home system
- an sftp client; this lets you transfer files back and forth using a graphical interface or command line
For more information, see Accessing Files Remotely
Connecting to Rutgers Only Resources via a VPN
Note: You do not need a VPN service for our major public systems like Blackboard, Canvas, Sakai, Box, Microsoft Teams, OneDrive, Rutgers Connect, (Office365), ScarletApps, WebEx, LinkedIn Learning, myRutgers portal etc.
If you are planning to connect to internal machines using Remote Desktop Service, the University recommends that you use the University Remote Desktops Gateway Service and not utilize the VPN for better performance.
VPN software extends your computer network connection as if you are connected to a remote network. For example, when you are connected to the Rutgers VPN server, your computer will appear as if it is on RUNet, enabling you to access all Rutgers services that are not available to the public. This VPN service is available to current Rutgers faculty/staff, guests, and students.
For instructions on using the new University VPN, see https://soc.rutgers.edu/vpn/. (You may have used an older VPN system. It will be decommissioned fairly soon.) Some notes on the VPN:
- This system requires you to activate the VPN service for yourself before you can use it. Go to netid.rutgers.edu, log in, and look for the [service activation] link as shown in the figure above. Click on [Remote access VPN…] and click on button at the bottom.
- If you aren’t currently using two-factor authentication (DUO), you’ll need to enable that. This is done at https://it.rutgers.edu/two-step-login/.
- Once that is done, follow the instructions at https://soc.rutgers.edu/vpn/ to install the VPN software on your system. It’s may not be obvious how to find the instructions to install the software on the web page. Pull down the menu in the black menu bar: “Virtual Private Network [VPN]” That will point to information for the various operating systems.
- Note that when the VPN is in operation, all network traffic except to your local network is routed through Rutgers. That means all of your web browsing, mail, etc, will go to Rutgers and then out to the Internet. It will go out through the Rutgers security scanning and NAT.
Advanced Users Only – Optional
For advanced users who are willing to do some work configuring their home systems, you might want to setup Kerberos at home to let you ssh to our systems without typing a password.
For help with our systems or If you need immediate assistant, visit LCSR Operator at CoRE 235 or call 848-445-2443. Otherwise, see CS HelpDesk. Don’t forget to include your NetID along with descriptions of your problem.

